Import ACSC Windows Hardening Policies in Intune - Step by Step Instructions
Step by Step instructions to create ACSC Windows 10 hardening settings in Intune using Graph API
Microsoft have published Intune policies to comply with Australian Cyber Security Centre's (ACSC) Windows 10 Hardening Guidance.
This policies are quite easy to import using graph explorer using official instruction provided at https://github.com/microsoft/Intune-ACSC-Windows-Hardening-Guidelines.
However, this guide provides detailed steps by step instructions and screenshots to simply this process.
To import these settings in Intune follow these steps
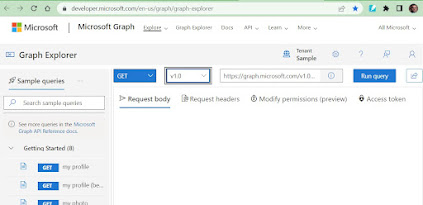
1. Navigate to Microsoft Graph Explorer.
2. Click on Sign in, login using authorised privileges in respective tenant i.e. Global Administrator
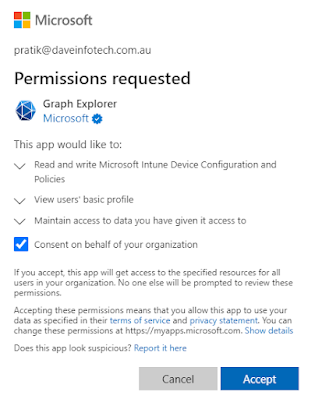
3. You may get a prompt to accept the consent, select Consent on behalf of your organization then click Accept.
4. Create a post request using Beta schema and type following query as shown in the screenshot,
https://graph.microsoft.com/beta/deviceManagement/configurationPolicies
5. Open new browser and go to ACSC Windows Hardening Guidelines policy and paste it in the request body
6. Go back to Graph Explorer and Paste the content in request body, modify the name value if required.
7. Go to Modify permissions(preview) and click Consent.
8. You will get a prompt to accept the consent, select Consent on behalf of your organization then click Accept.
You will receive the error if permissions are not granted.
9. Click Run Query to create the configuration profile in Intune tenant. You will notice green tick in couple few seconds.
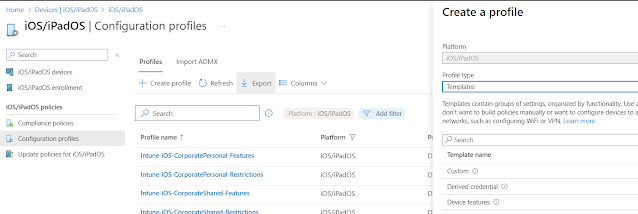
10. You can to to Intune Portal to see the newly created ACSC Windows Hardening Configuration profile and you may complete the assignment to apply this policy to Windows device.
11. You may open the settings and make changes as per your requirements.
12. Copy/Paste other ACSC JSON policies and paste in Graph Explorer to complete creation of policies in Intune.
- Windows Security Baseline (for use with ACSC Windows Hardening Guidelines)
- ACSC Windows Hardening Guidelines-Attack Surface Reduction
- ACSC Windows Hardening Guidelines-User Rights Assignment
- Upload UserApplicationHardening-RemoveFeatures.ps1 powershell script to Intune Portal
- Upload OfficeMacroHardening-PreventActivationofOLE.ps1 powershell script to Intune Portal
- ACSC Office Hardening Guidelines
- All Macros Disabled or Macros Enabled for Trusted Publishers - As per the requirements.
- ACSC Edge Hardening Guidelines
13. Once you complete the policies import, you will see following setting are enabled in the Intune tenant.
Check out following link for more information.














Comments
Post a Comment