Setup single sign-on to Apple devices apps and websites that use Microsoft Azure AD for authentication
Configuring Microsoft Enterprise SSO Plug-In for Apple Devices:
The Microsoft Enterprise SSO plug-in enables
users to sign in to apps and websites that rely on Microsoft Azure Active
Directory (Azure AD) for authentication, including Microsoft 365, using a
single sign-on (SSO) process. This plug-in utilizes the Apple single sign-on
app extension framework to minimize the number of authentication prompts that
users receive when accessing devices managed by Mobile Device Management (MDM).
Additionally, any MDM that facilitates configuring SSO profiles is supported.
After configuring the Microsoft Enterprise
SSO plug-in, apps that support the Microsoft Authentication Library (MSAL)
automatically integrate with it. However, apps that don't support MSAL can also
utilize the extension, such as browsers like Safari and apps that use Safari
web view APIs. To do so, simply add the application bundle ID or prefix to the
extension configuration.
For example, you can enable a Microsoft app
that doesn't support MSAL by adding com.microsoft. to the AppPrefixAllowList
property. It's crucial to be cautious about which apps you allow to use this
feature, as they will bypass the interactive sign-in prompts for the signed-in
user.
Prerequisites
- The device is managed by Intune.
- iOS/iPadOS 13.0 and newer
- The Microsoft Authenticator app must be installed on the device.
A
Step-by-Step Guide.
1. After logging into your endpoint.microsoft.com account, navigate to
the Devices section, select iOS/iPadOS, and click on Create Profile under Configuration
Profile. From there, choose Templates and then select Device Features.
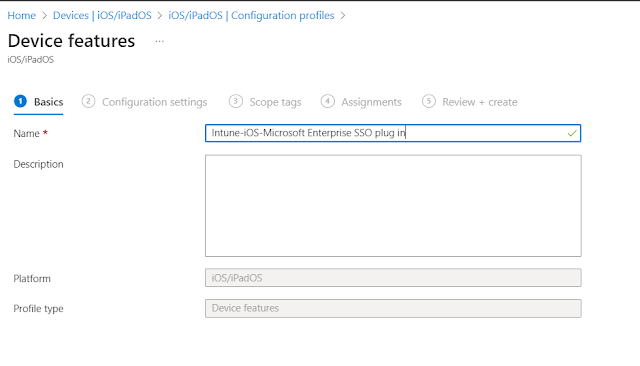
2. Once you have created the profile, give it a
name and then click on Next.
 3.Once you click on Next, you will be directed
to configure the profile. From there, you will need to modify the Single
Sign-On App Extension and change the SSO extension type to Microsoft Azure AD
3.Once you click on Next, you will be directed
to configure the profile. From there, you will need to modify the Single
Sign-On App Extension and change the SSO extension type to Microsoft Azure AD.PNG) 6. Once you have completed all of these steps,
you will need to assign it to either a group or a device.
6. Once you have completed all of these steps,
you will need to assign it to either a group or a device.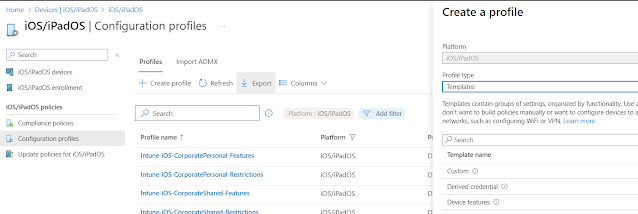

.PNG)


Comments
Post a Comment